Research Work on Advanced Cyber Threat Intelligence by Easytech4all.net enters Global Internet Ranking. In the league of Extraordinary Worldwide Cybersecurity Solution and Service Providers.
Global Cyber Defense Threat Intelligence Organisations . Power Webinars & Brainstorms
CYBER CONFERENCE & COUNTERING RANSOMWARE
200 Plus Video Playlist on Cybersecurity and Advanced Cyber Defense Threat Intelligence

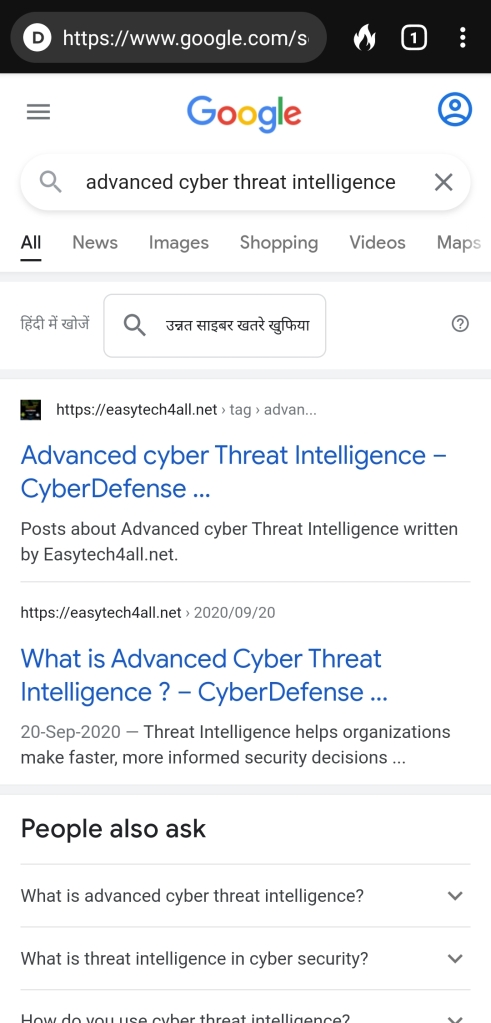
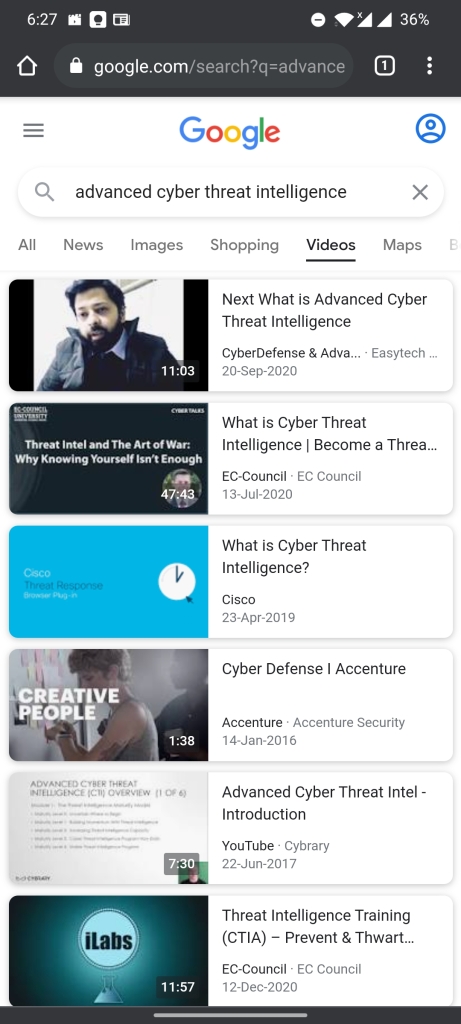
Mapping Global Ranking for Advanced Cyber Threat Intelligence
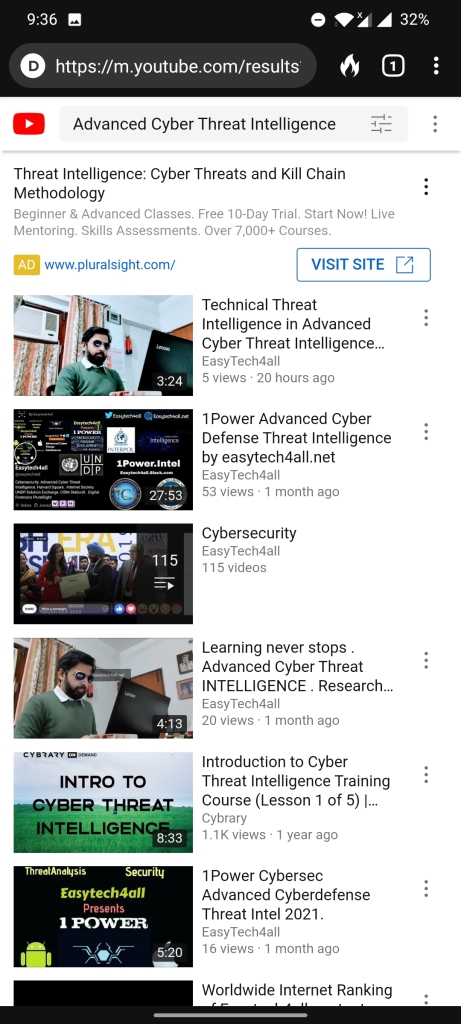
Youtube listing under Advanced Cyber Threat Intelligence for Easytech4all
Twitter Ranking Under Advanced Cyber Threat Intelligence.
Cloud Archives.
Defense Grade Security Intelligence,Awareness,Forecasts,Strategy.
Research and Reports.
Simplifying Complex Pieces of Incredible Intel.
CyberSec Trends. Vulnerability Statistics.
US DOD Enterprise Security.
Email Threat Analysis.
Data Breach Industry Forecasts.
UK National Cybersecurity Reports.
Adversary Threat Hunting.
Protecting Digital Assets.
Advanced Persistent Threat Analysis (APT)
CyberCrime Modus Operandi and Statistics.
Nation State Security Trends.
National CyberPower Reports.
Age of Cyber Warfare.
Research reports on Advanced Cyberdefense Threat Intelligence by US Department of Defense , US Navy , National Cybersecurity Alliance , CrowdStrike , Edgescan etc.





The MOOC LMS Nanocertifications and Webinars that facilitated essential knowledge acquisition in the field of Cybersec.
Performing Visual Data Analysis of Computer Security Attacks in real time.
Adding Voice over to LMS project on Cyberdefense Threat Intel.
CyberSec KnowHow 2.0
Splunk Enterprise Security Solutions.A software product that enables you to search, analyze, and visualize the data gathered from the components of your IT infrastructure or business. Splunk Enterprise takes in data from websites, applications, sensors, devices, and so on. After you define the data source, Splunk Enterprise indexes the data stream and parses it into a series of individual events that you can view and search.
Essential Paradigms for Cybersecurity.
Mapping CyberAttacks for second quarter of 2020.
Importance and value is Cybersecurity in India.
Observations and resource recommendations in Cybersecurity.
Computational research in advanced cyber Threat Intelligence .
Highlights of cutting edge Research in Cybersec and infosec.
Long Journey of Accreditations , Certifications , webinars , Research , observations and experience in Cybersec , infosec , threat Intel.
1Power.Intel CyberDefense Research to mitigate harmful events in Cyberspace.
ComSec Protocols and Paradigms.
Visual CyberSec Research through infographics.
Monitoring CyberAttacks through real time intelligent Maps.
Data Protection and risk mitigation
A Night in the life of CyberDefense Researcher.
Investigation of the biggest CyberAttack on World’s Leading CyberPower
https://easytech4all.net/2020/12/24/biggest-cyberattack-on-worlds-leading-cyberpower/
Lightning Fast Cybersecurity updates in real time.
https://flipboard.com/@easytech4all/cybersecurity-6tbejh5oz
Follow Blog for work in progress updates on R&D
https://easytech4all.net/author/easytechonline/
Cybersec YouTube playlist.
https://easytech4all.tumblr.com
https://twitter.com/easytech4all
cybersecurity
cyberattacks
Cyberattack
cybersec
infosec
dataprotection
dataprivacy
linux
cyberdefense
cyberdefence
AdvancedCyberThreatIntelligence
CyberThreatIntelligence
technology
informationtechnology
easytech4all
cybersec
Cyberdefense
Cyber Defense
Cyber Defence
easytech4all
Cybersecurity
infosec
Advanced cyber threat Intelligence
cyber threat Intelligence
Data privacy
Data protection